Given the popularity of such platforms like WordPress or Joomla for developing online content and the multitude of websites and blogs created by these means, it is essential for the authors and administrators of these platforms to follow some basic safety procedures to safeguard themselves and consequently, the websites they relate to. One of the important solutions in this respect are VPNs – these can ensure online privacy and significantly enhance the safety of online users, including those that manage the site.
VPNs As A Safety And Privacy Solution For Website Creators And Managers
There are a multitude of providers to choose from that offer a balanced combination of high safety standards, great access speeds, a vast number of VPN servers around the world, and great additional features. A good starting point into the world of VPNs is the bestvpnrating resource, which contains useful information about the basics of the technology, the typical usage scenarios, the features offered by different providers (so that a comparison or an in-depth evaluation of each provider is possible), etc.
How Do VPNs Ensure Safety
VPNs establish secure communication channels between the users and the Internet – these channels always have the VPN server as an intermediary node and the user always adopts the IP address of the VPN server (abandoning his/her own) just like with proxy server, or using vpn download. Unlike with a proxy server, however, all the data sent and received by means of the created communication channels are encrypted using strong encryption protocols and keys. This leads to virtually absolute anonymity for the VPN user.
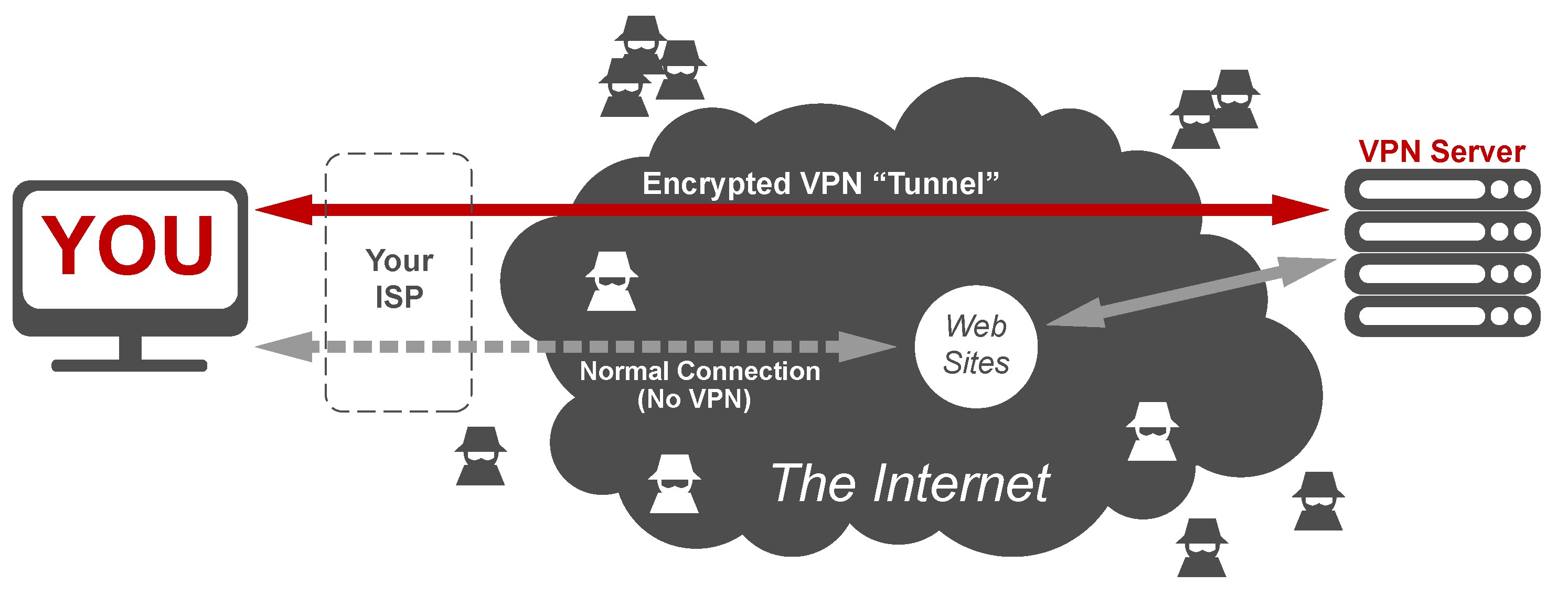
When using a VPN, logging in into the admin panel of the site by any power user that can manage the site or create content (e.g.WordPress) can be done anonymously. Given the encrypted communication and the rerouting of the traffic through the VPN server, hackers can find it very hard to intercept and decode this communication, making hacking attempts on each of the listed entities harder.
Of course, there are attacks that can be carried anyway, like DoS (resulting in a temporary shutdown of the site), or attacks on the servers used by the website, so VPNs are rather to ensure the safety of traffic communications at the user end and between the user and the server. Even so, it is worth mentioning that the user would still be vulnerable to other threats (such as phishing, accidentally installed malware or spyware, Trojan viruses, etc.). Hence, for a truly comprehensive security, safe practices must be adopted, as well as antivirus products and firewalls.
VPNs Abolish Country-Specific IP Bans
Given that the VPN server can be located anywhere in the world, this allows users to appear as residents of any of the countries from a list of choice (typically, this list is vaster for a paid rather than a free VPN service). This fact can be of great relevance to website creators and admins. Thus, users with VPNs from all other the world can adopt the desired IP address and bypass country specific IP bans imposed by site managers/admins (the latter is normally done out of financial, safety, or practical considerations – e.g. an abnormal number of hacking attempts or spam messages from a given country).
Consequently, admins and other power users must be aware of this possibility and must base their judgments accordingly. A user registration system could be implemented which utilizes the phone number of the user (in order to increase the chances that the visitor is a true resident of the given country).
Typical Features To Look For In A VPN Provider
Encryption Strength And Overall Speed
There is a wide choice of VPN providers that constantly try to outcompete each other, constantly refining their standard package of security-related features (or other kinds of features) but also adding innovative ones. One of the key priorities for any VPN provider is the encryption strength, which is defined by the strength of the encryption key (256 bit vs 128 bit) and the strength of the encryption protocol.
The following protocols are common to date among VPN providers:
- OpenVPN – this is an open-source protocol that brings very strong universal encryption for all activities, although with some activities, it can feel a bit slow at times. Nevertheless, it is one of the most preferred encryption protocols and therefore, it must be a priority that the chosen VPN provider supports this protocol among others;
- L2TP/IPSec – another very popular protocol, ensuring good encryption and access speed, but easy to block because of the reliance on a single port;
- SSTP – this one brings high-security standards and is also difficult to block or detect;
- IKEv2 – this is a simpler protocol, that makes it easier to be used with smartphones, while also ensuring great speed (a few open source implementations are available);
- PPTP – it is fast and widely supported but much less secure, which makes it usable for basic activities, such as streaming and browsing (if no sensitive data is involved).
As it can be noticed, the strongest encryption comes with lower speeds and the opposite (this is due to the extra time required to process the information).
The Kill Switch
Another important security-related feature in a VPN is the availability of a kill switch. The cause that motivated this features is the following – any VPN, at times, can get overloaded and when this happens, the traffic might temporarily drop and lose encryption which can reveal the real IP of the user (IP leak). If a kill switch is implemented, this will kill the connection every time it drops preventing IP leaks and preserving user anonymity.
Anonymous DNS Servers
DNS resolution is the process that translates the letter-based web address into the corresponding IP address used for navigation. By default, the ISPs perform this translation process for most clients but this does not have to be so. Thus, an additional layer of privacy offered by many VPNs is represented by a dedicated DNS module to perform this translation anonymously away from the ISP.
Log Policy
Although they help hide this information from the Internet, VPN providers often store a number of details about their users in dedicated log files (the type and amount of detail vary hugely and can include financial credentials used for payments, IP addressed, session history, user-related data, etc.). Sometimes, details more than half a year old can be found in these logs and there is always the potential that these can be accidentally leaked online (or the servers can be hacked).
Given that even the resolution of the user’s monitor can prove useful in tracking his/her online activity, it is obvious that one should look for a VPN service that stores as little user data as possible (however, care must be taken, provided that these details are usually burrowed deeply in the user agreement text). Also, remember that there is always the possibility that authorities might pressure a given provider to pass this information to the government (this is especially concerning in countries with authoritarian regimes, where even a “legal” decision can be easily obtained in this respect).
Type Of Devices And OSs covered
With the advent of smartphones, tablets, and various other gadgets, one has to ensure protection across an entire spectrum of operating systems (often, different versions) and device types. While in case of devices that only connect to the home WiFi network, it would suffice to just implement a VPN on the WiFi router alone, for portable Internet-capable devices, one would have to ensure standalone installations of the VPN software.
The reality is that many of these devices (smartphones, tablets, laptops, etc.) are often used to access multiple networks including public ones. Consequently, it makes sense to opt for a VPN subscription that covers a suitable number of devices of each specific category you are interested in. This would likely involve systems running Android, iOS, Windows, etc.
To conclude, VPNs are powerful tools to ensure online privacy and to further boost online safety. Given that a relatively large and dynamic website needs to be managed by multiple people (admins, content creators, other power users), it is imperative to implant safe practices among these and one such practice is the use of VPNs. It is important to keep in mind that any vulnerabilities affecting one user, can end up affecting the entire website.
In case you want to find out more about VPNs, head to Bestvpnrating.com, where you can build the necessary literacy in the field, can learn more about the potential use scenarios that are of relevance to you, but also can contrast different providers in order to choose one that is most suitable for your needs.
About the author
Dainan Gilmore is an enthusiastic expert in cybersecurity and works as a Cryptanalyst for the Bestvpnrating.com.
- Resolving the “Class JFactory Not Found” Error in Joomla When Upgrading to J6 - December 19, 2025
- The Utility Of VPNs For Site Authors And Admins - November 24, 2025
- Joomla! 6: What’s New and How to Upgrade from Joomla! 5 - October 23, 2025








Recent Comments